Technical Blog
Software Updates on i.MX8MP, Part 2: Mender & Yocto Project
How to build a basic image for an Olimex iMX8MP-SOM using Yocto Project, and use Mender.io to manage and deploy over-the-air (OTA) updates to embedded devices
July 30, 2024/by Konsulko Group
Software Updates on the i.MX8MP, Part 1: qbee and RAUC
Learn the exact steps to build a basic image for an Olimex iMX8MP-SOM using Yocto Project release 5.0 LTS, and to perform a software update using qbee and RAUC.
July 22, 2024/by Konsulko Group
Build an image and perform updates with RAUC on Rockchip
Konsulko Group's Leon Anavi, maintainer of meta-rauc-community, ported RAUC to Radxa Rock Pi 4 Model B, the first Rockchip device supported in the community.
June 26, 2024/by Konsulko Group
Porting Mender to Raspberry Pi 5 and Yocto Project Scarthgap
A practical guide outlining the exact steps to build a Mender-enabled image for Raspberry Pi 5 and execute an A/B update using the latest Yocto Project release.
May 17, 2024/by Leon Anavi
Integrating RAUC with Yocto Project on BeagleBone Black
Exact steps how to integrate RAUC with Yocto Project and OpenEmbedded for booting from a microSD card on BeagleBone Black.
January 30, 2024/by Leon Anavi
Mender Add-ons: Remote Troubleshooting Devices in the Field
Mender offers several add-ons. These are optional extensions that provide functionality for use cases beyond the core OTA updates features.
April 3, 2023/by Konsulko Group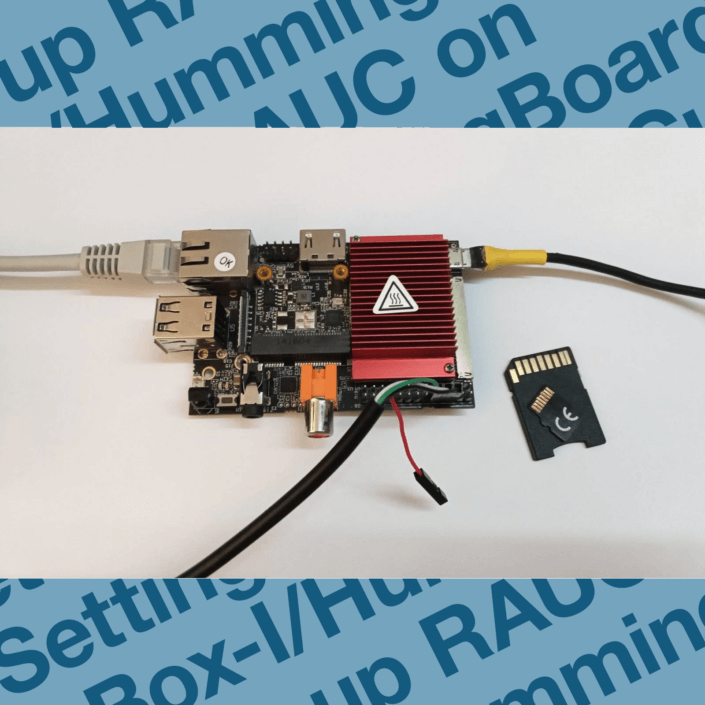
Setting up RAUC on CuBox-I/HummingBoard for Software Updates
A popular solution to provide OTA (over-the-air) updates for Embedded Linux devices, RAUC requires advanced skills for initial integration.
February 16, 2023/by Konsulko Group
Using kernel config fragments to remove an unwanted feature
How to remove a standard kernel feature when it causes an embedded system to lock-up on either warm reboot or shutdown, preventing over-the-air (OTA) updates
February 21, 2022/by Tim Orling